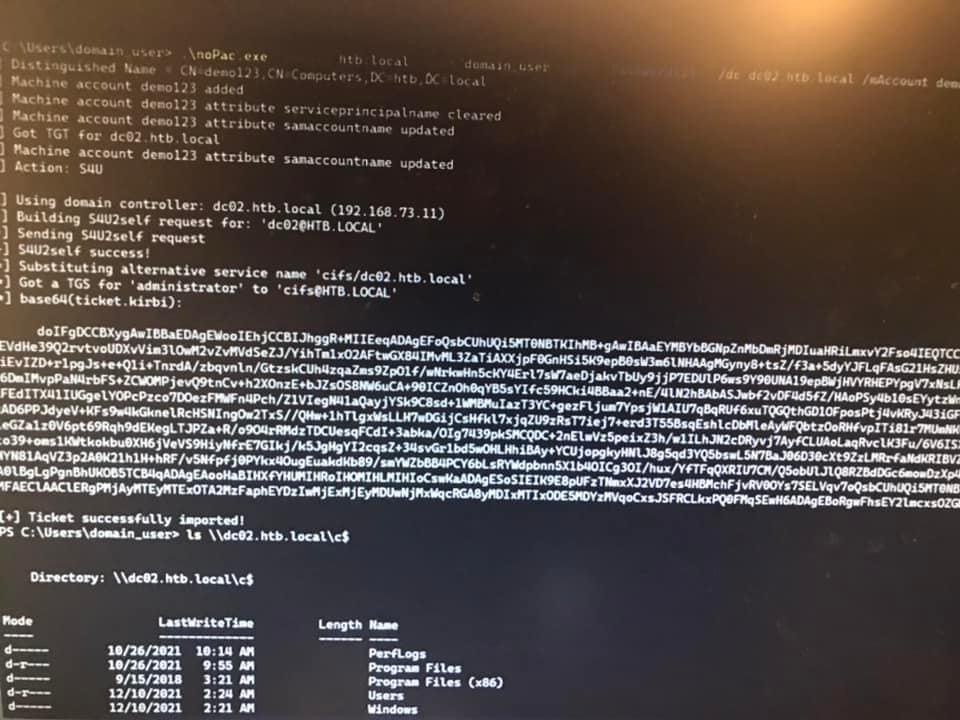
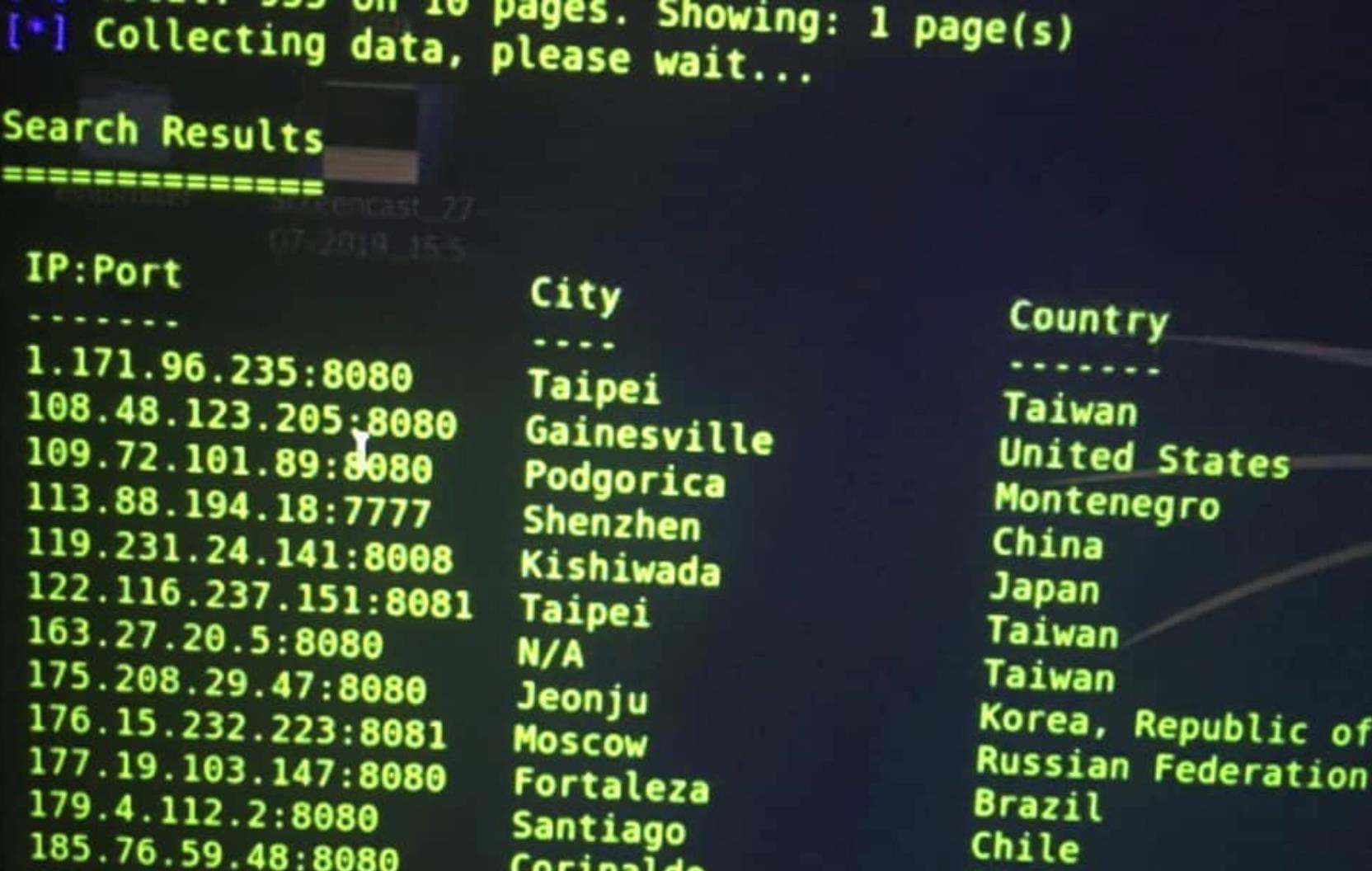
This log4j (CVE-2021-44228) vulnerability is extremely bad. It only took 5 minutes. Millions of applications and platforms use Log4j for logging, and all hacker need to do is get the app to log a special string. So far Apple services/devices, government websites, Facebook, Microsoft platforms, Android, banking apps, Playstation 4 and 5, Xbox 360, Xbox Series S, Gmail, Hotmail, iCloud, Steam, Minecraft and other MMPORG games have all been confirmed vulnerable. So make sure you update all devices when updates are available, don't wait. I was also able to track IP addresses from some malicious actors (evidence shown below). The CISA, Pentagon and Dep of Homeland & Security warned other foreign governments and companies to patch it as fast as possible. Exploitation can be achieved by a single string of text, which can trigger an application to reach out to a malicious external host if it is logged via the vulnerable instance of Log4j, effectively granting the adversary the ability to retrieve a payload from a remote server and execute it locally. Tracked as CVE-2021-44228 and by the monikers Log4Shell or LogJam, the issue concerns a case of unauthenticated, remote code execution (RCE) on any application that uses the open-source utility and affects versions Log4j 2.0-beta9 up to 2.14.1. The bug has scored a perfect 10 on 10 in the CVSS rating system, indicative of the severity of the issue. It's not the question if coordinated attacks will happen, it's just a matter of time. A large part of the internet got exposed. Given the ease of exploitation and prevalence of Log4j in enterprise IT and DevOps, in-the-wild attacks aimed at susceptible servers are expected to ramp up in the coming days, making it imperative to address the flaw immediately. Multiple firms released a fix called "Logout4Shell" that closes out the shortcoming by using the vulnerability itself to reconfigure the logger and prevent further exploitation of the attack.
Source Michael Tillerson on Facebook : https://www.facebook.com/100010218787043/posts/1558352884515323/?d=n
*Beware click the link!

 Murtad methamphetamine
Murtad methamphetamine
 Sandidi
Sandidi
 ImamWawe
ImamWawe